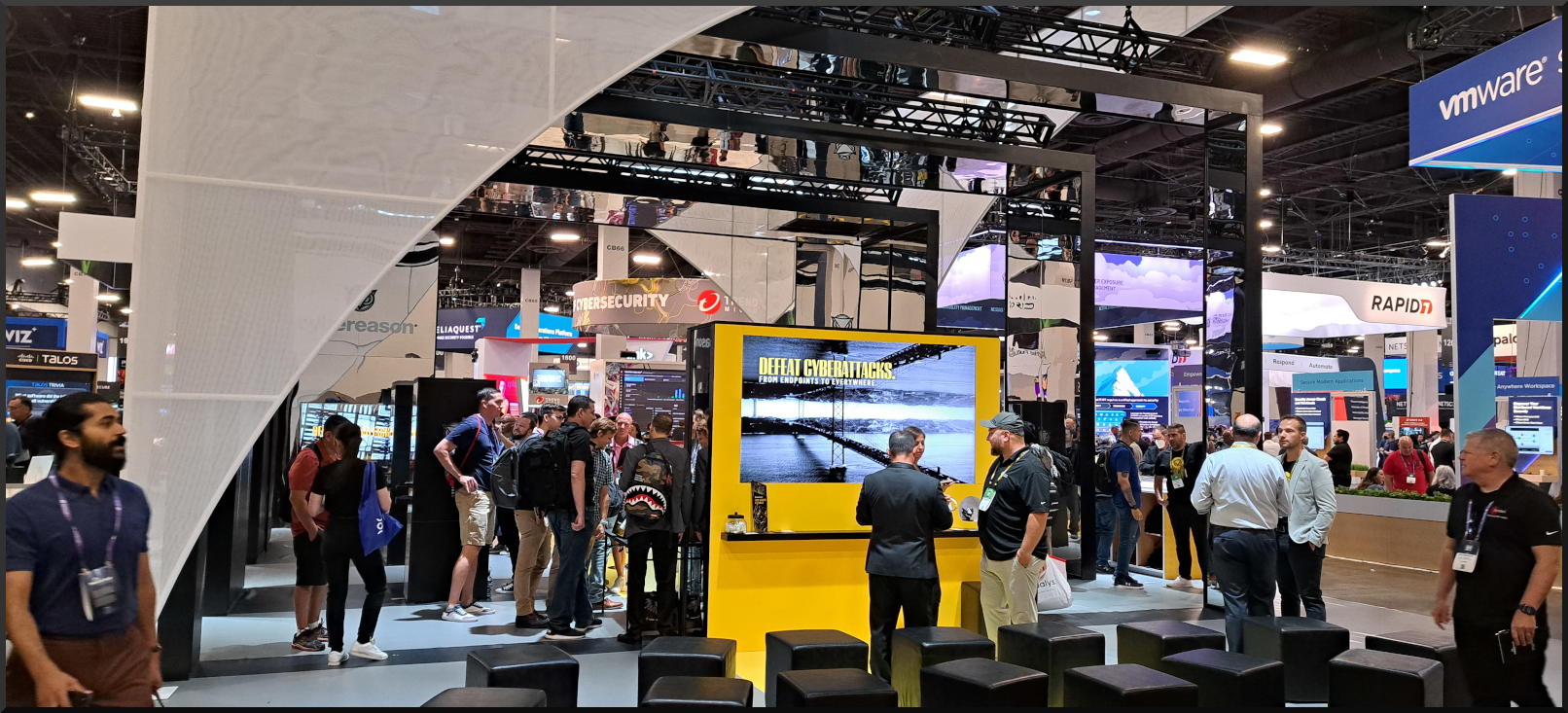
I finally did it! I went to Blackhat USA. The experience was more than I could have ever imagined. There were ups, downs, and it was a lot of physical and intellectual work. Hearts were broken, then pieced together. The Conference Associates put in work! Any show of this magnitude would require it in order to make it flow as smoothly as it did. It wasn't until the flight back to Chicago that I grinned and said, "that was fun". I left Blackhat feeling stronger, smarter, less of an imposter (syndrome), and ready for growth. Over the course of a few days, I had the opportunity to meet peers that I had never before seen in real life! It reminded me of the old IRC days. You know, back when meeting up was 'rare' but speaking daily was common.

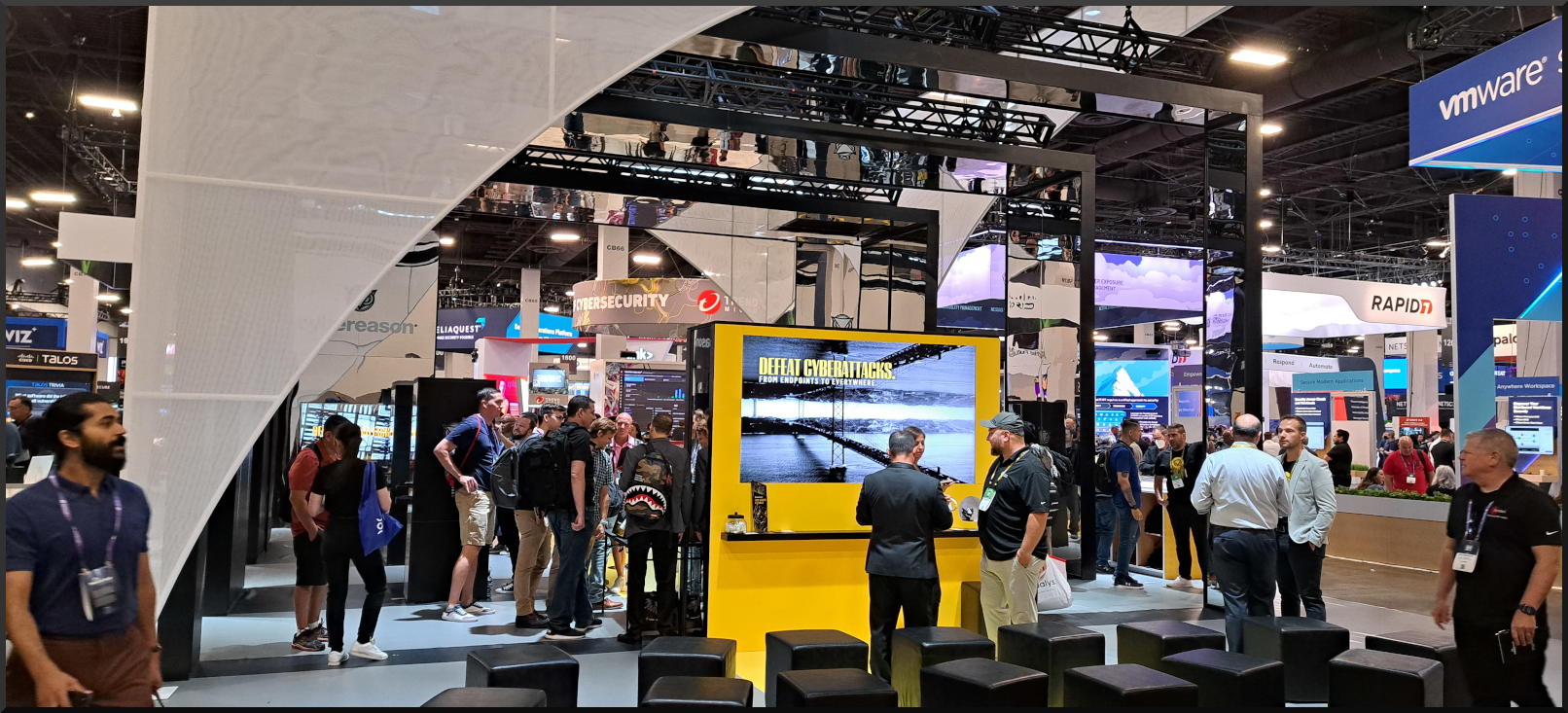
I did a lot of walking but, to say "it was worth it" would be an understatement. I was able to speak on new vulnerabilities at a technical level and learn about the projects people were working on. Away from work. The infosec community is the true definition of '6 degrees of separation'. Everybody knows every other person through somebody else, and 97% of the time it was the result of a positive previous interaction. The ability to communicate with other information security professionals, from all over the world, has really given me a greater appreciation for 'where' people come from and what those unique perspectives add to the community overall.

Unique cultural and social experiences intertwined with security create a repository of knowledge that is extremely relevant and 'in the ballpark' when new attack vectors are developed. Some conferences acknowledge these communities within a community, on con days, with "villages" and themed social events. Communication is one of the greatest assets of the information security culture. The deeper you dive into security, the more 'niche' topics become. The only way to fill those niche gaps is by having a diverse pool of candidates in the pipelines.
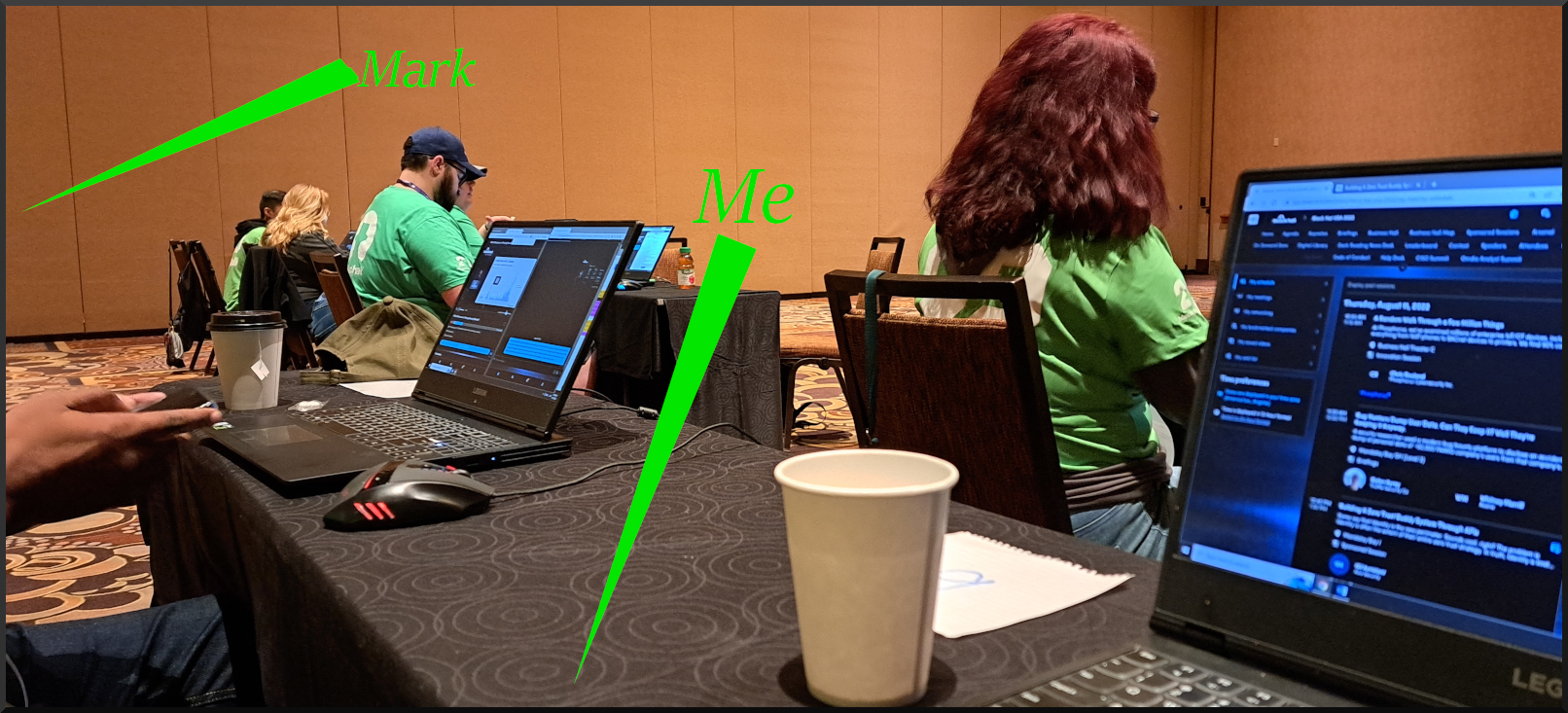
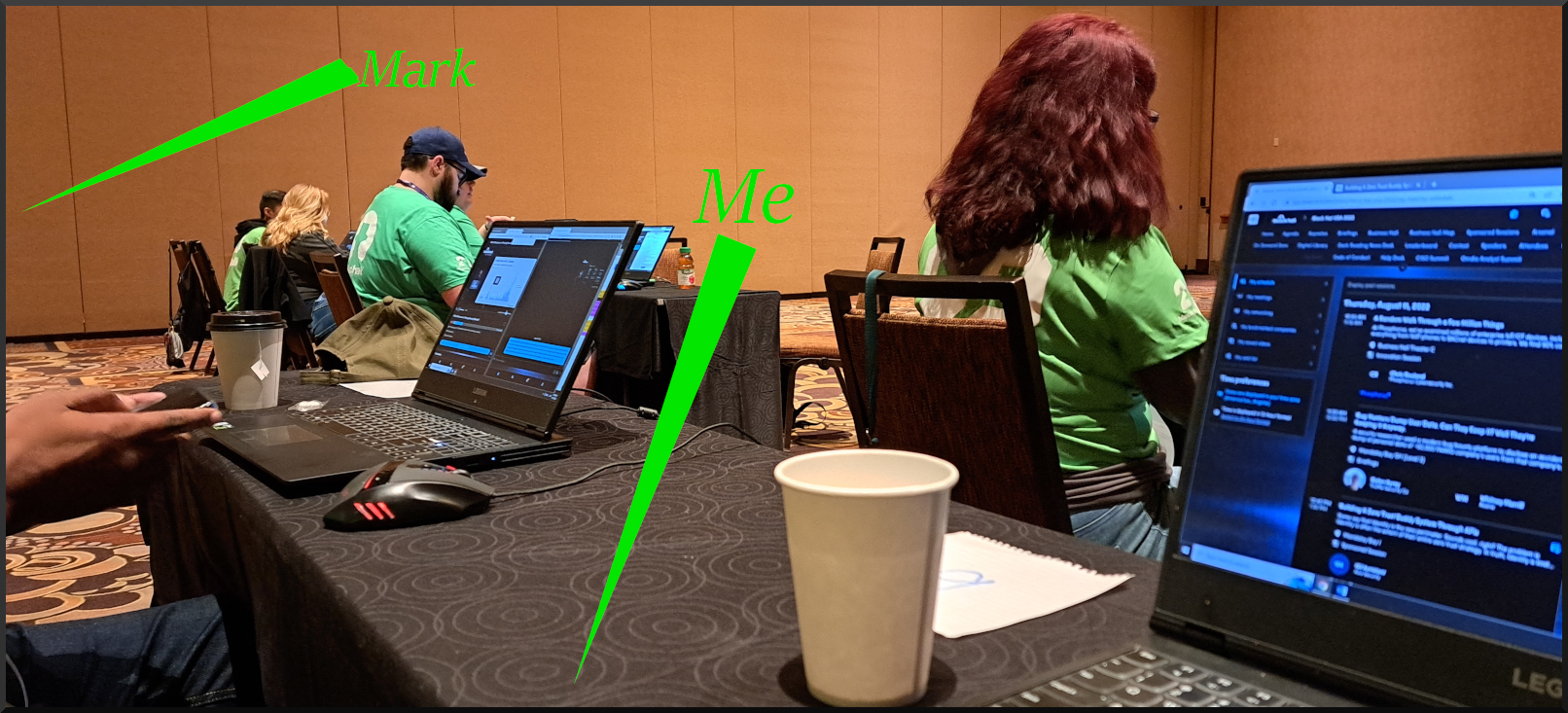
[When I needed 'off feet' time I was able to assist with the session chat monitoring. Great conversations were had with all the people in this room. Mark included!']

[National Cyber League dinner;]

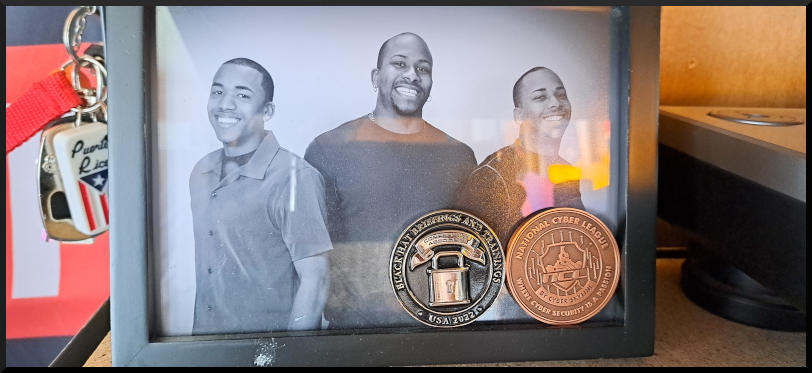
[Rapid-7 event : We 'captured' our buttons and had a great time.[Jose, Paul, Erik pictured {CCC CA Spring 2022/National Cyber League Team}]

At the end of it all I was able to add some new badges to my collection and a challenge coin.
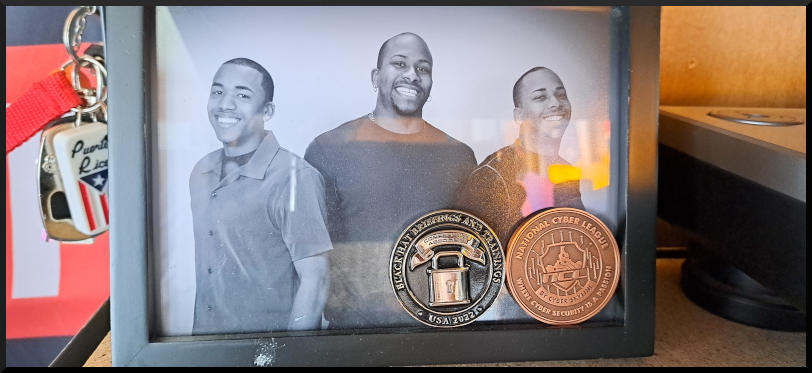
Unfortunately I was not able to stay for the DEFCON Conference.
This is the closest i'll get to DEFCON this year.

[Erik, Yo, Charlotte, Paul pictured {CCC CA Spring 2022/National Cyber League Team}]

[Erik, Yo, Jose, Paul pictured {CCC CA Spring 2022/National Cyber League Team}]


[City Colleges of Chicago Cyber Security Career Accelerator Class of Spring 2022 --image coming soon]
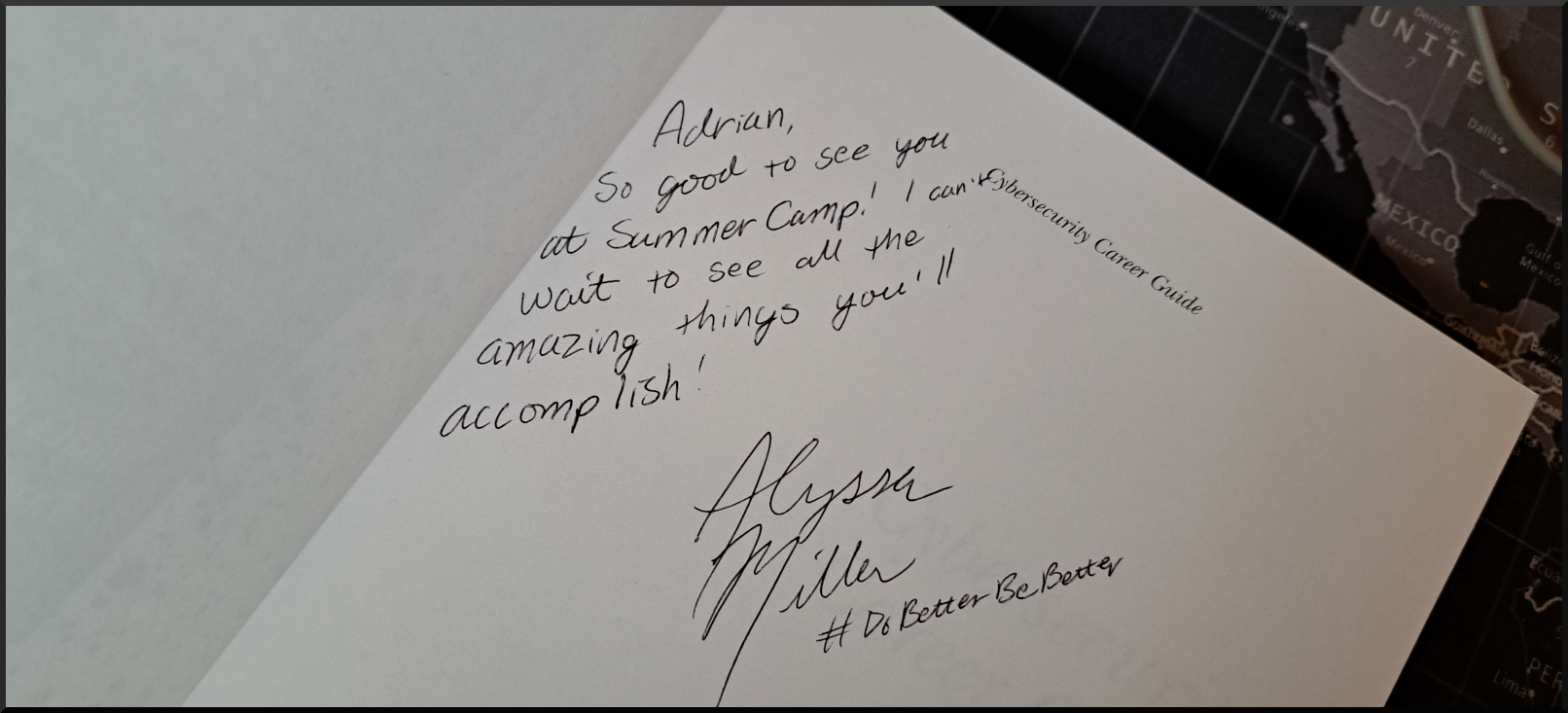
My goal is to align myself, professionally, so that these events are more relavent and more beneficial to my career development while simultaniously making meaningful NEW relationships and connections. I'm going to do better and be better! Thank you Alyssa Miller. Thank you Mishaal Khan.
#hackersummercamp
Special thanks to Casey w/ Blackhat, Chris Lemon: My CCC CA instructor and NCL coach, and all City Colleges of Chicago classmates and program organizers! I will be forever grateful for the opportunities and experiences.
City Colleges of Chicago: Take notice of the successes and opportunities created by your unique approach to cybersecurity programs. These programs are created and continually refactored by individuals that do a lot more than what can be documented or quantified. I have many "CCC" CompTIA IT certifications and have said thank you louder than the schools ever have to the facilitators [IMO]. Retain talent. Retain the community. Build up. This is the future of education.
- A. Buford
- Aug, 2022
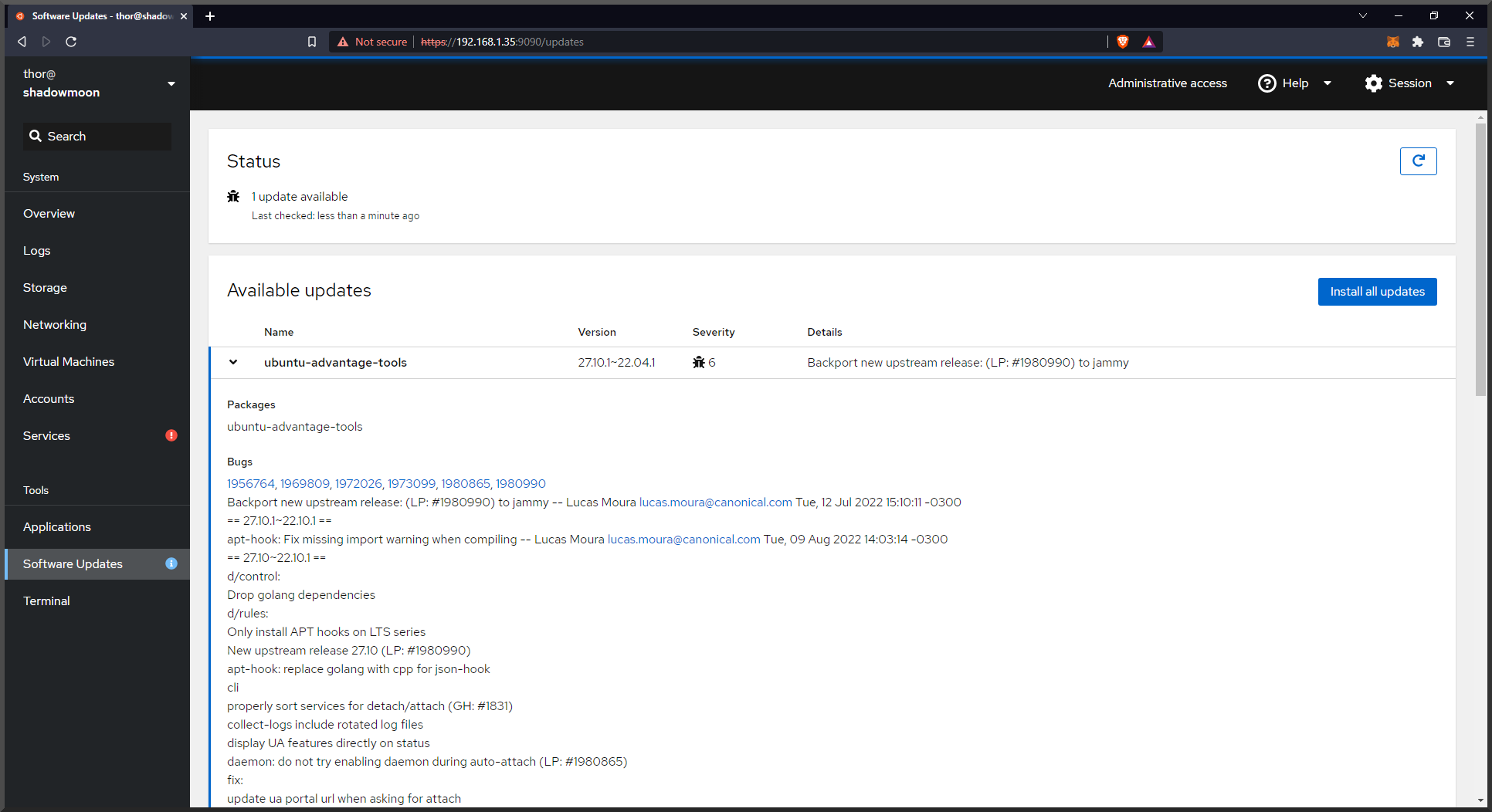
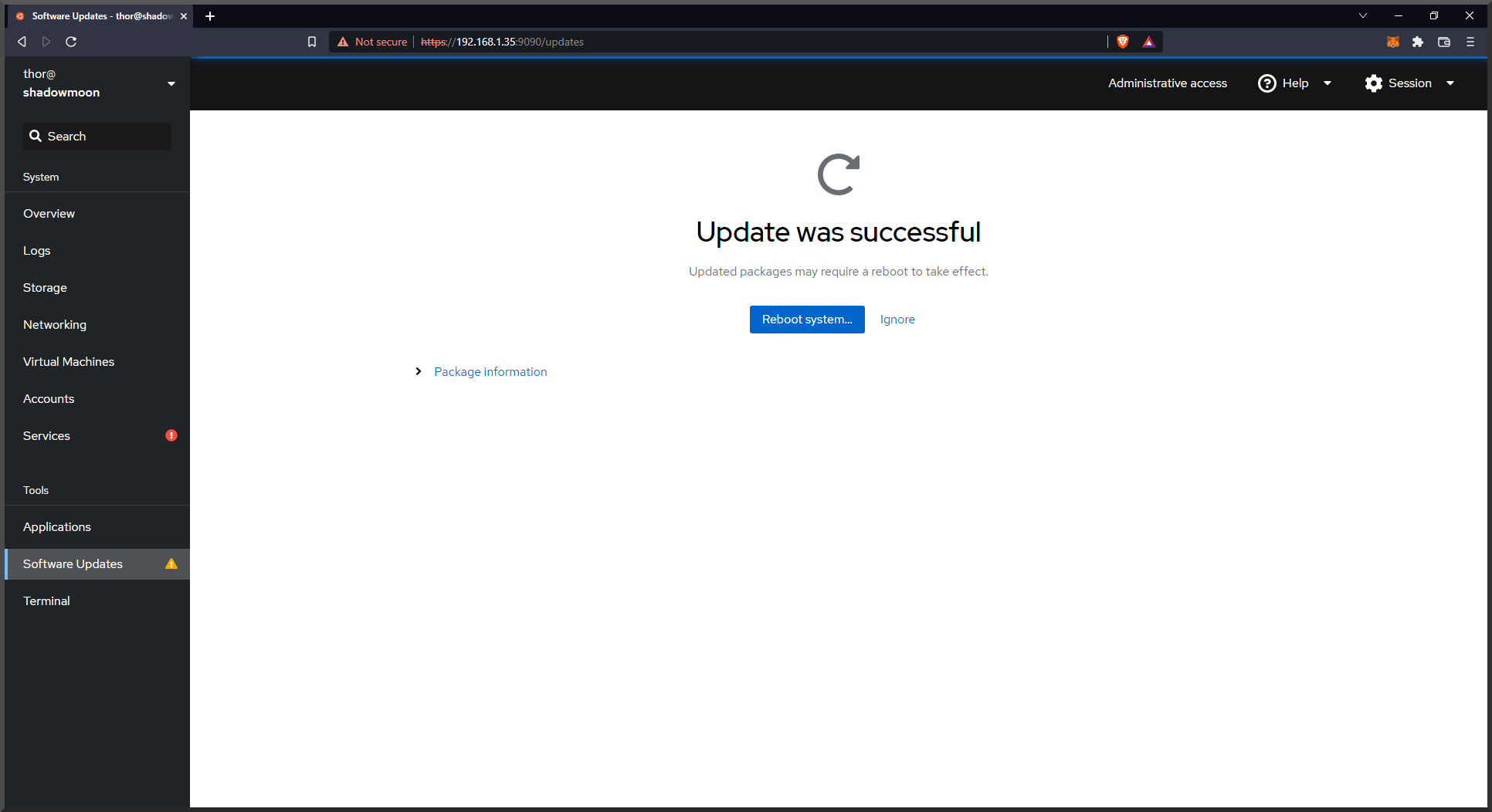
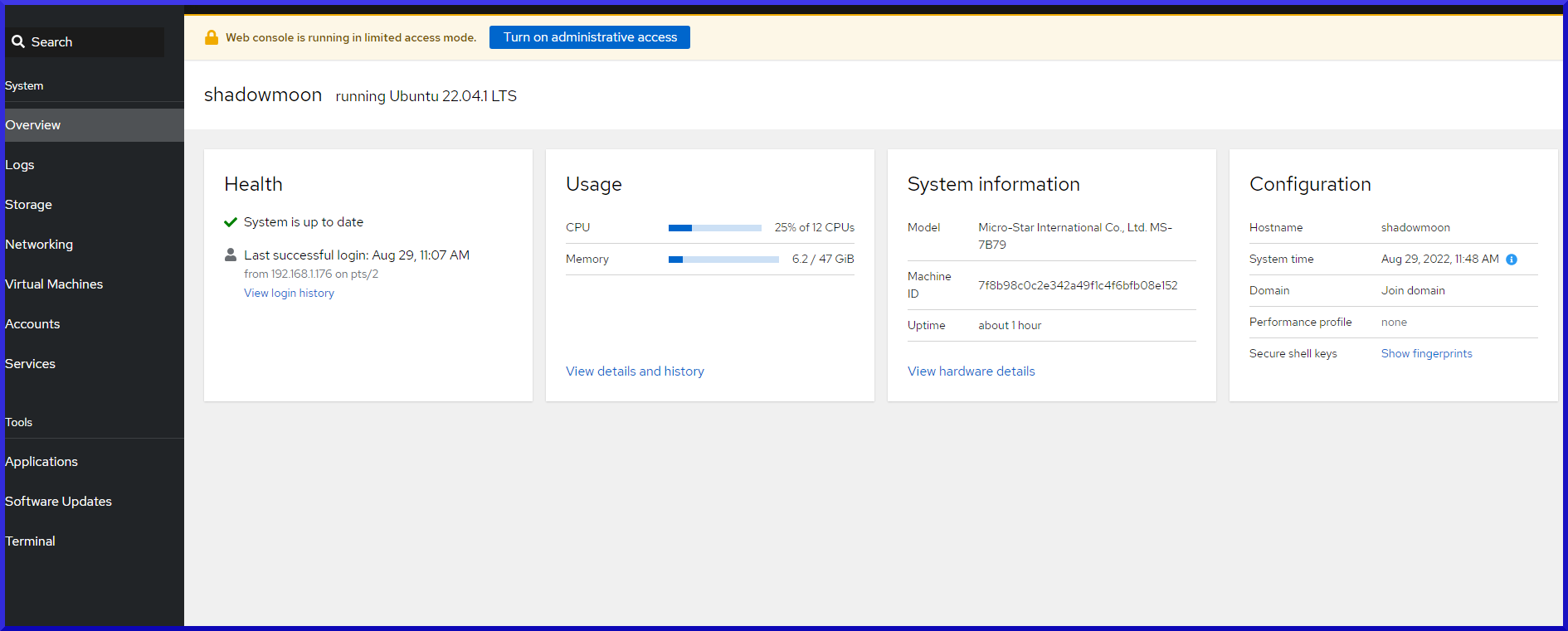
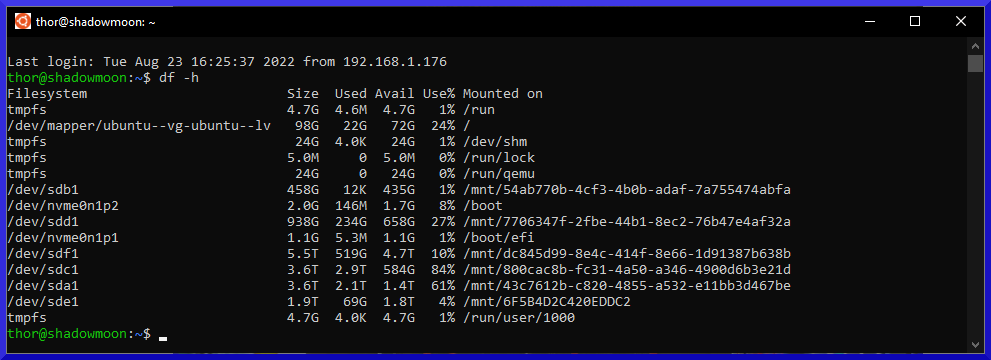
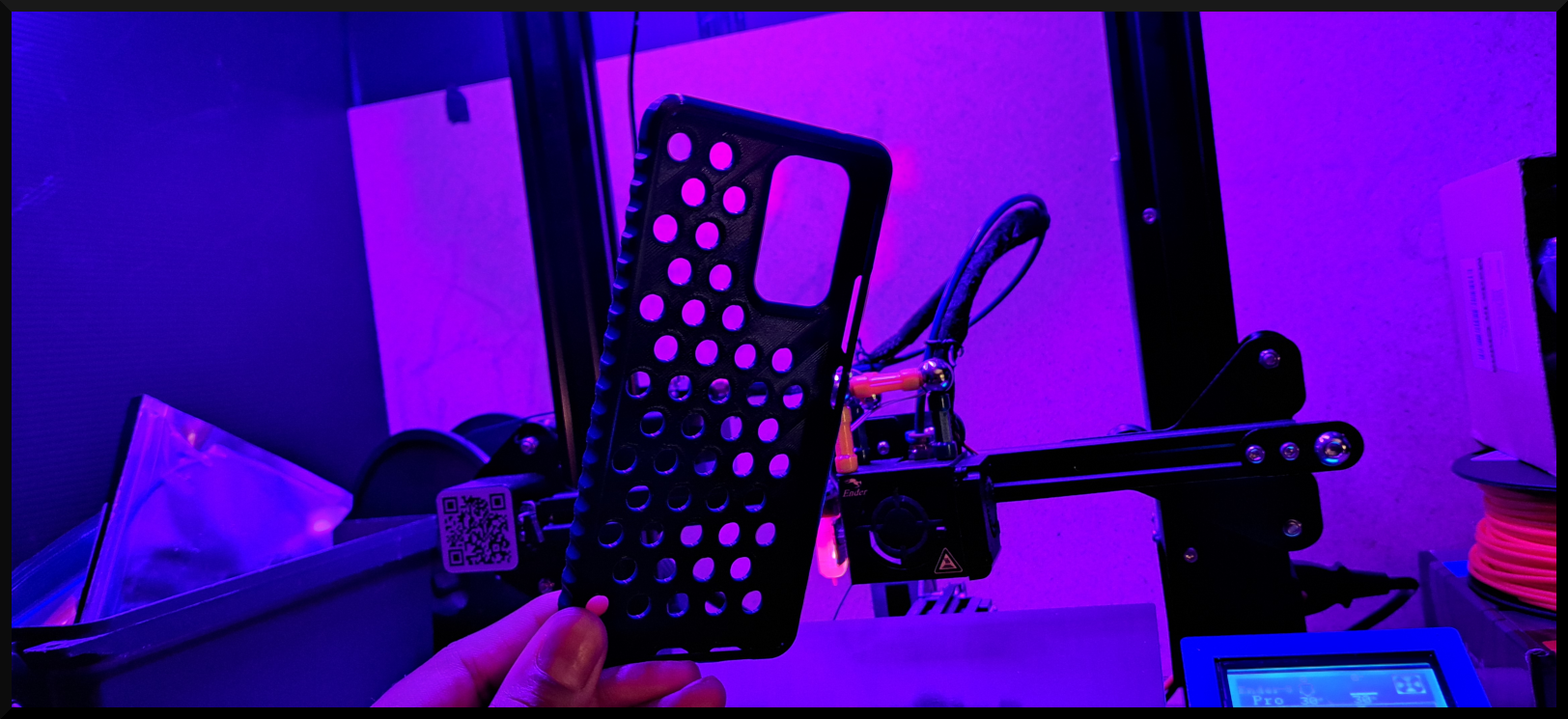
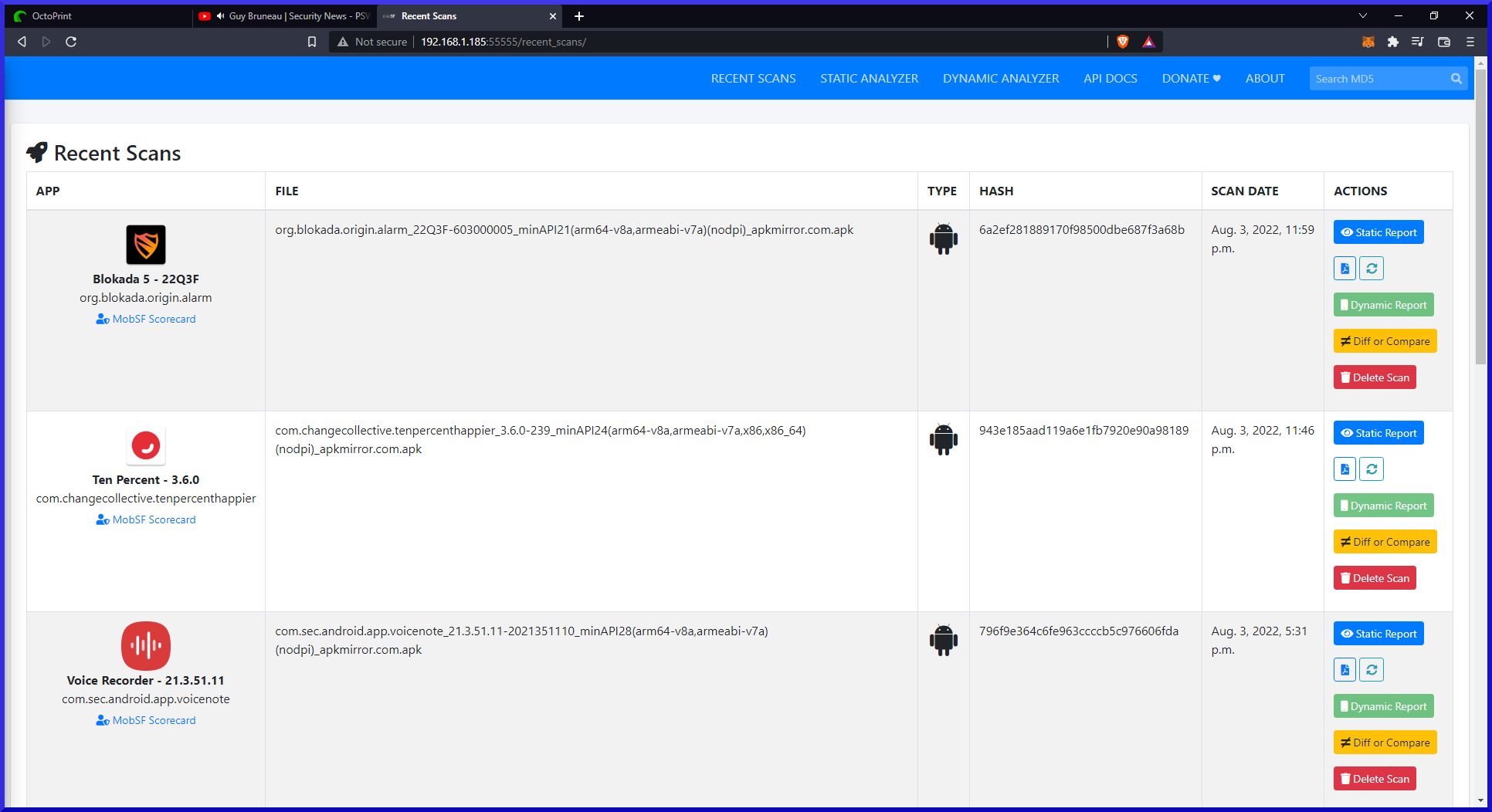
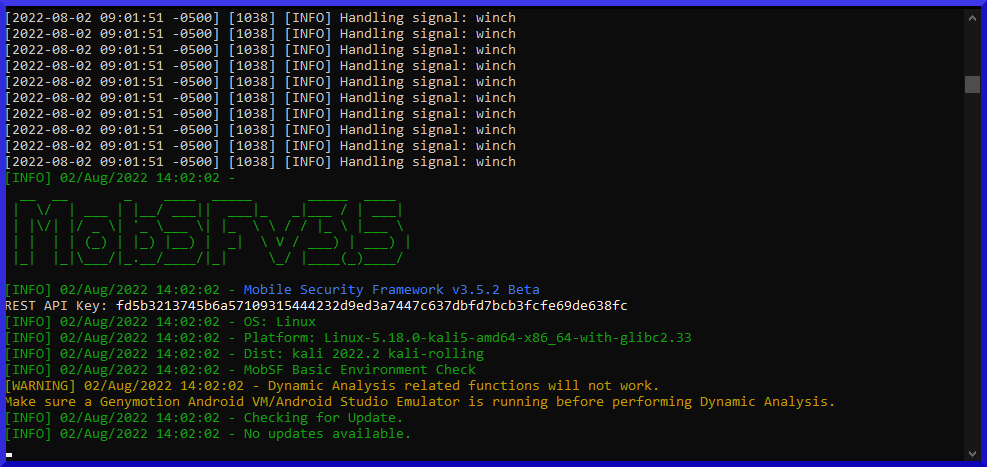
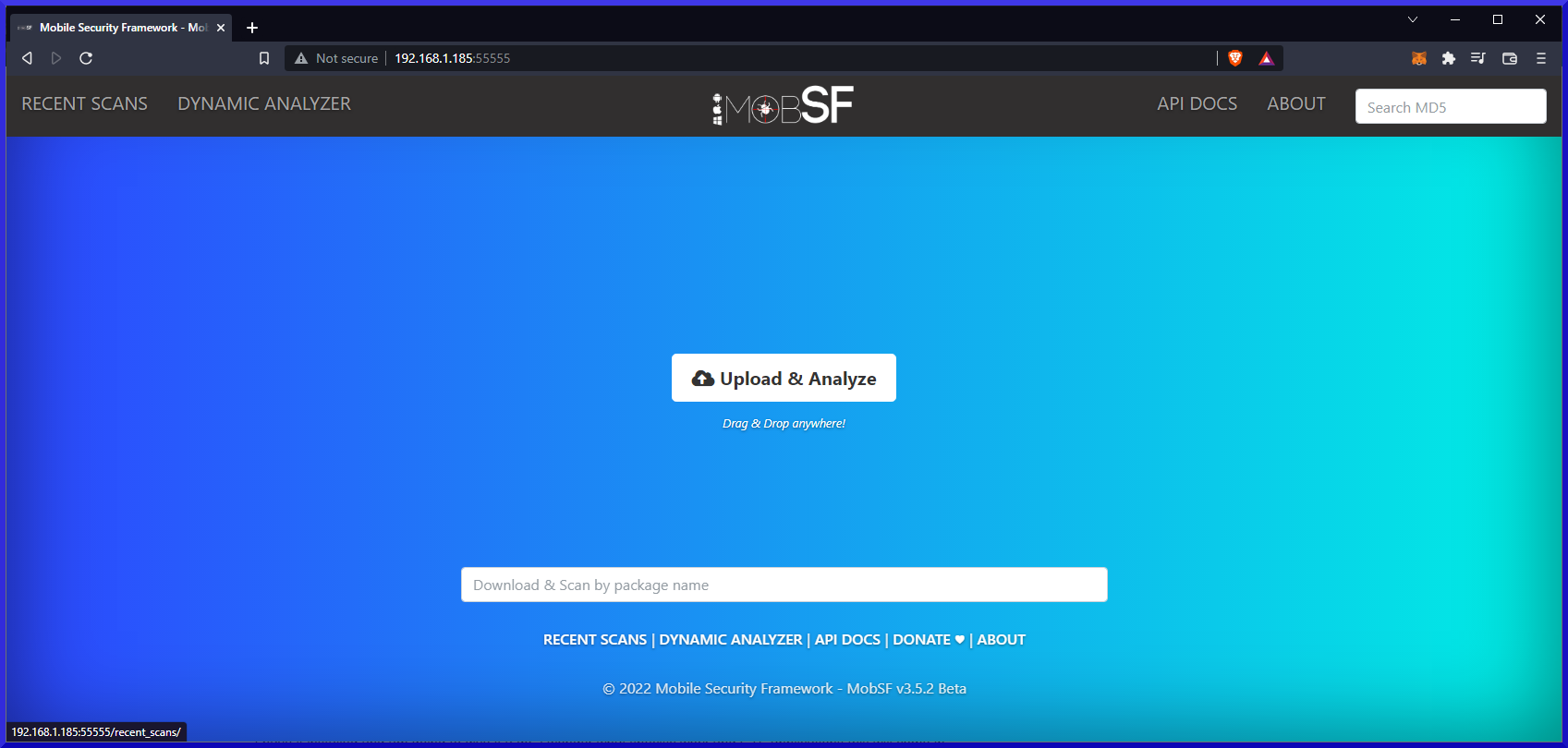
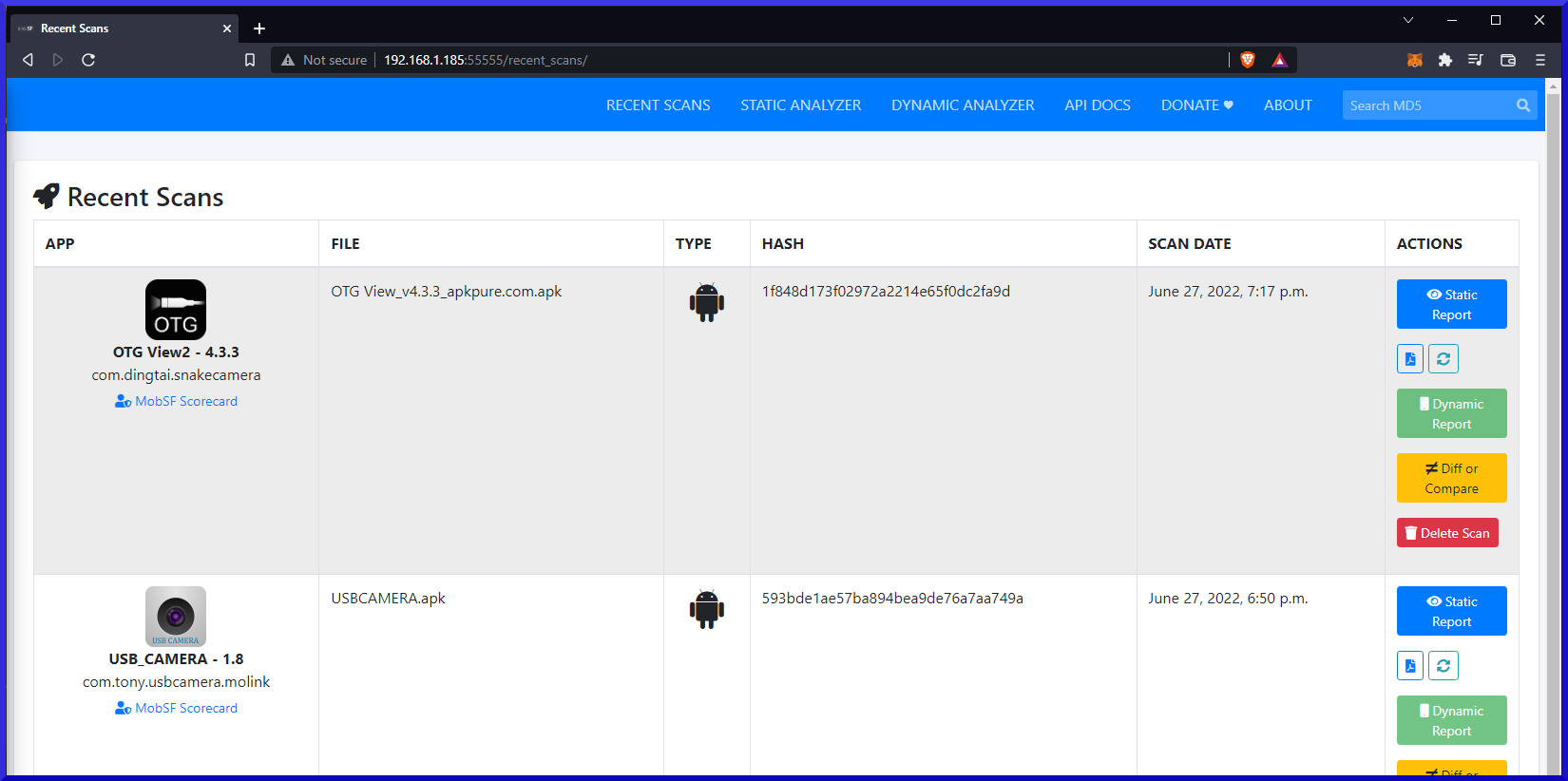
 I have a couple concerns with Cockpit currently. The first being the web ui defaulting to http vs secure https. I know the fix will be to create self-signed certificate(s) and place in correct directory.
I have a couple concerns with Cockpit currently. The first being the web ui defaulting to http vs secure https. I know the fix will be to create self-signed certificate(s) and place in correct directory.