hidden
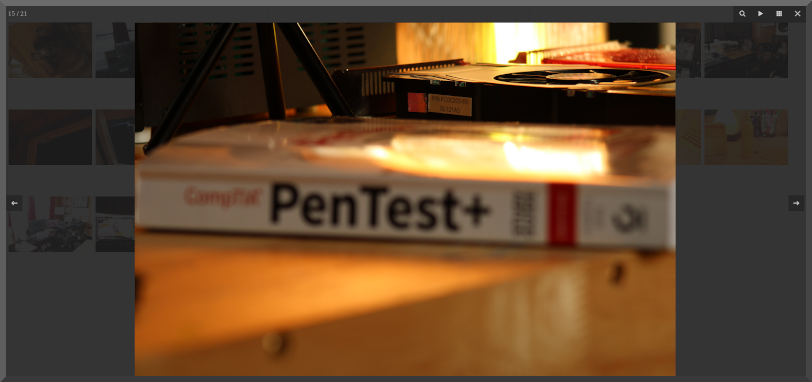
CompTia Cloud+: On to Chapter 4. Slow down tiger.
CompTia Cloud+: @pg 103, 33%(ish) done
CompTia Cloud+: @pg 62
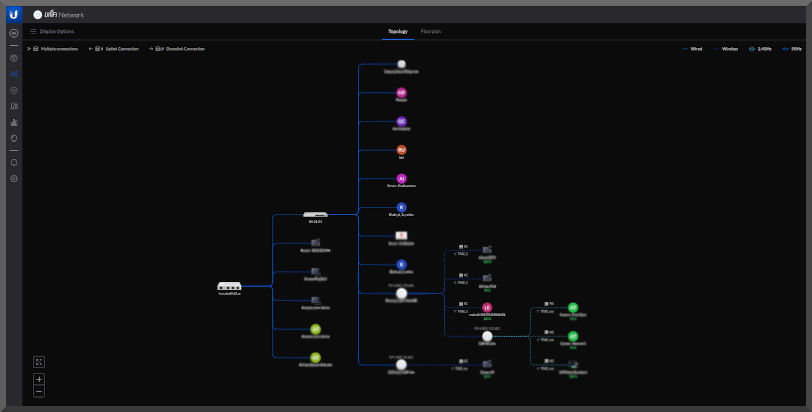
Home network topology like whoa
CompTia Cloud+: Here I come.
"Wegmans discloses a data breach, customers information was exposed on the Internet due to a misconfiguration issue."

Takeaways 1. Hackers can't stop won't stop 2. Maybe these supermarket chains are the low hanging fruit 3. Documentation indicates passwords were 'hashed' but no mention of any 'salting' or randomization.
The hashing part really got to me. Considering that any APT will eventually add new hashes to their rainbow tables it creates a 'matter of time' type situation when it comes to security. Most people re-use passwords. Yes there is some confusion regarding what the RockYou2021 password database is and isn't but i'd wager a super-sparkle-penny that 70% of ALL passwords are in there.
Update 6-22-21 : Passwords were salted AND NOT included in breach. I was told to shut my darn mouth and will.
"Report: CVS Health Exposed Search Records Online"
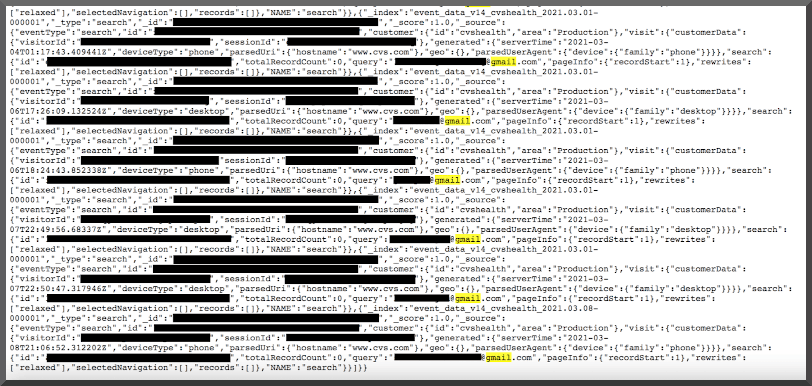
Takeaways 1. Nobody else will protect your data better than you can 2. The databreach atmosphere with regard to politics is still the same. No accountability. 3. Only you can prevent forest fires
A little dev goes a long way

"Google’s June security bulletin addresses 90+ bugs in Android and Pixel devices."
1. Android is one of the most widely used opperating systems and will always be targeted 2. Is it really more dangerous to carry cash vs money on a cell phone? 3. That Google Pixel is very nice.... but it has so many CVEs specifically associated with it.
When you get that little notification to Update or Postpone it is a GREAT idea to update.
"Microsoft June 2021 Patch Tuesday addresses 6 zero-days actively exploited "
1. Wow that is a lot of 0-days for a single patch Tuesday. 50 vulns in total 2. Google's Project Zero really does find a lot of vulns. I don't think that will ever change 3. Privilege esc is still the way to go for bug bounties
Stay updated and stay patched. If it isn't supported then it might not be worth the keep.
"Department of Justice Seizes $2.3 Million in Cryptocurrency Paid to the Ransomware Extortionists Darkside"
1. Cryptocurrency is a matter of national security 2. The US gov is very deeply involved in the cryptocurrency darknet 3. Threat actors, such as Darkside, are going to restructure payment methods 4. Attacks against the national infrastructure will not be taken lightly
I am extremely proud of what our law enforcement agencies were able to accomplish. It really does send a powerful message to others thinking this attack-type would be their next pay day. Great job yall
Today : My 8yr old will learn to make a webpage, HTML
Smarter criminals : The white-hat researcher within
What is research? A gallery story
1. Self hosted
2. Retains EXIF data
3. Automatic/periodic sync w/o manual effort
4. Nice layout of images
4. Compatable with most browsers
I started by doing what every sane IT professional does and checked github to see if there was anything aleady created. There was a ton. None that fit my application specifically though. May of those projects, with good reason, had a lot of security baked in which resulted in many lines of code I didn't want to vet. It really does take a fine comb. The reason security was incorporated in approximately 90% of them was because of the ability to 'upload' by web users. That can obviously be a huge security dilema. Just imagine a threat actor hosting images, with embedded data, on a website that (unknowingly) doubles as a Ransomeware C&C server. That would be a bad time for any host. However, for our scenario, local users will be the only persons needing to add photos to our galleries. Right? I decided to narrow the scope to something more simple and came up with a PHP based idea.
Once I got the functionality and layout down on a whiteboard I went online for PHP code syntax help. This is 3 hours down the rabbit hole later. While doing so I realized (YET AGAIN!!!!) this was no new idea and that W.S. Toh created something over at Code-boxx that solved the problem.... a few months ago. I simply place my images, from any device on the LAN, into a shared network folder. Every XX minutes, via a cronjob, the folder is synced to a dev env (Example from similar deprecated script rsync -avzhe ssh /mnt/91337b30-484d-472b-90ec-c193e34b8893/public_nas/farm/2g.dsm.ecu.removal/xxxx.buf0rd.com.syncd.gallery/ user@XXX.buf0rd.com:XXXXXXXXXXX). In the dev env is a cronjob to sync with the cloud provider (after running various checks).
TDLR; Researching any topic can end up taking up a ton of time. That is why most organizations hire externally. They simply do not have the bandwidth to teach internal employees the skillsets needed to allow an internal empoyee to research, design, and implement a new 'technology'.
Also, the website has new image 'Content' galleries
Own YOUR SERVER

Why don't you post more often
A child's brain is amazing
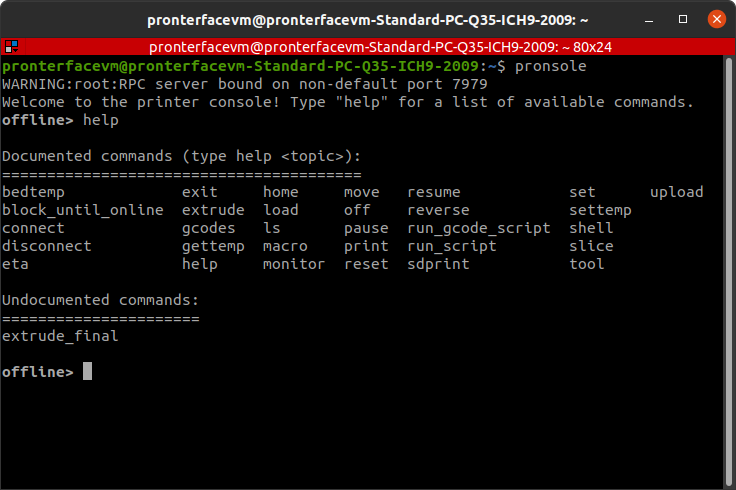
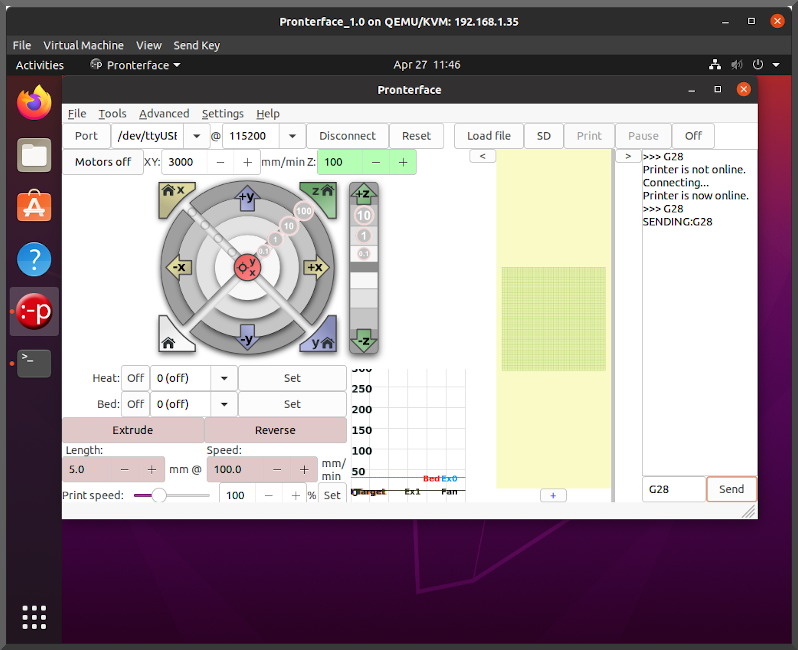
Pronterface and Pronsole.. because people are lazy
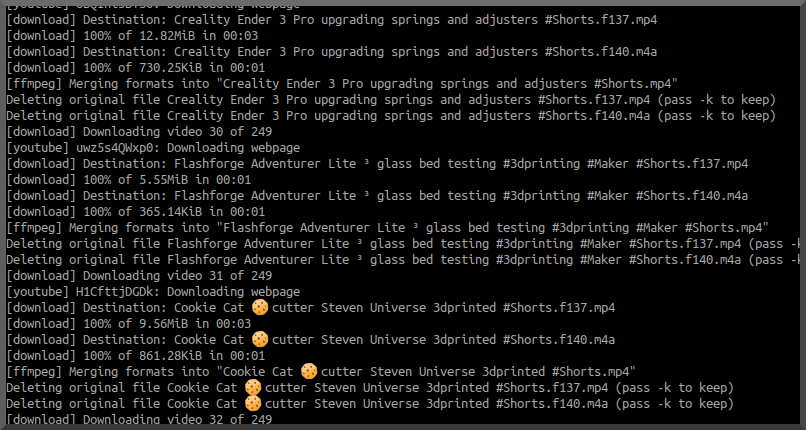
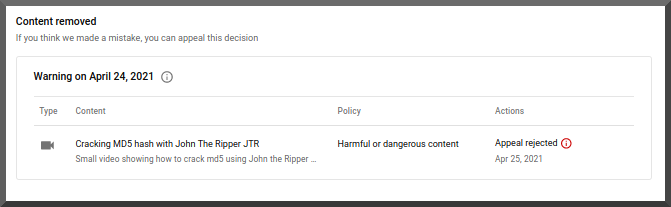
Dear YouTube, you played yourself
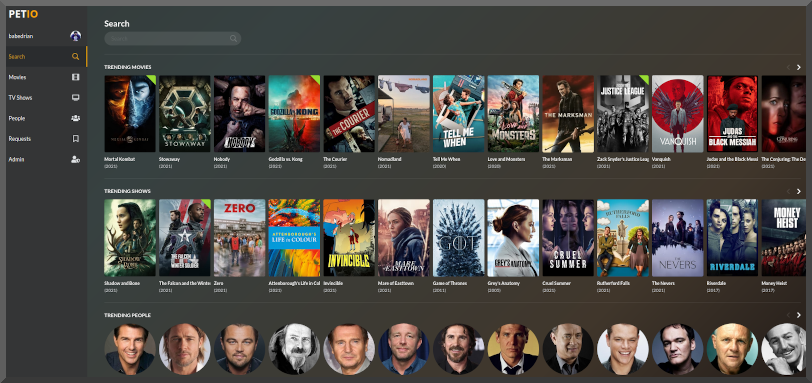
Installed Petio for the PLEX Server
Chicago Virtual Cybersecurity Summit 2021

Image Galleries for all.
BalBot v1.00 | Raspberry PI to hotspot internet tetherer
#!/bin/bash
ifconfig eth1 down
ifconfig eth0 down
iptables -f
# Enable IPv4 and IPv6 forwarding (feature):
sudo sysctl net.ipv4.ip_forward=1
sysctl net.ipv6.conf.default.forwarding=1
sysctl net.ipv6.conf.all.forwarding=1
# Assign IP address to eth1:
ip link set up dev eth1
ip addr add 10.42.0.1/24 dev eth1
ip link set up dev eth0
ip addr add 10.43.0.1/24 dev eth0
# Packets forwarding wlan0 -- eth1:
iptables -t nat -A POSTROUTING -o wlan0 -j MASQUERADE
iptables -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
iptables -A FORWARD -i eth1 -o wlan0 -j ACCEPT
iptables -A FORWARD -i eth0 -o wlan0 -j ACCEPT
@reboot with a slight delay (sleep 15;)
The power of plants.. Not those kind

Trace Labs OSINT QEMU/KVM Installation video created!
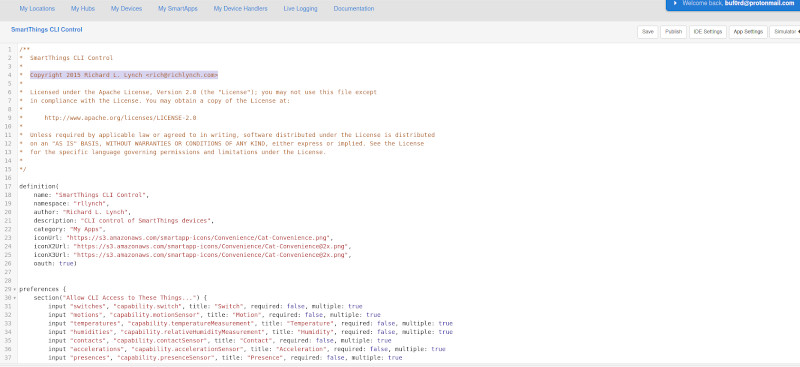
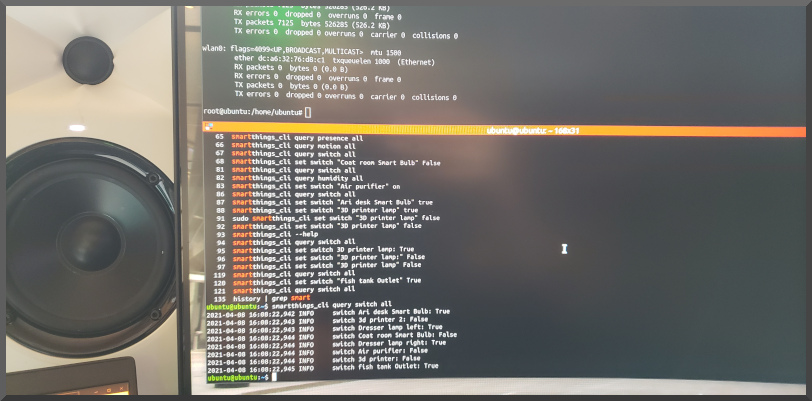
SmartThings via CLI
 Chapter #5 completed. Good amount of new material.
Chapter #5 completed. Good amount of new material.